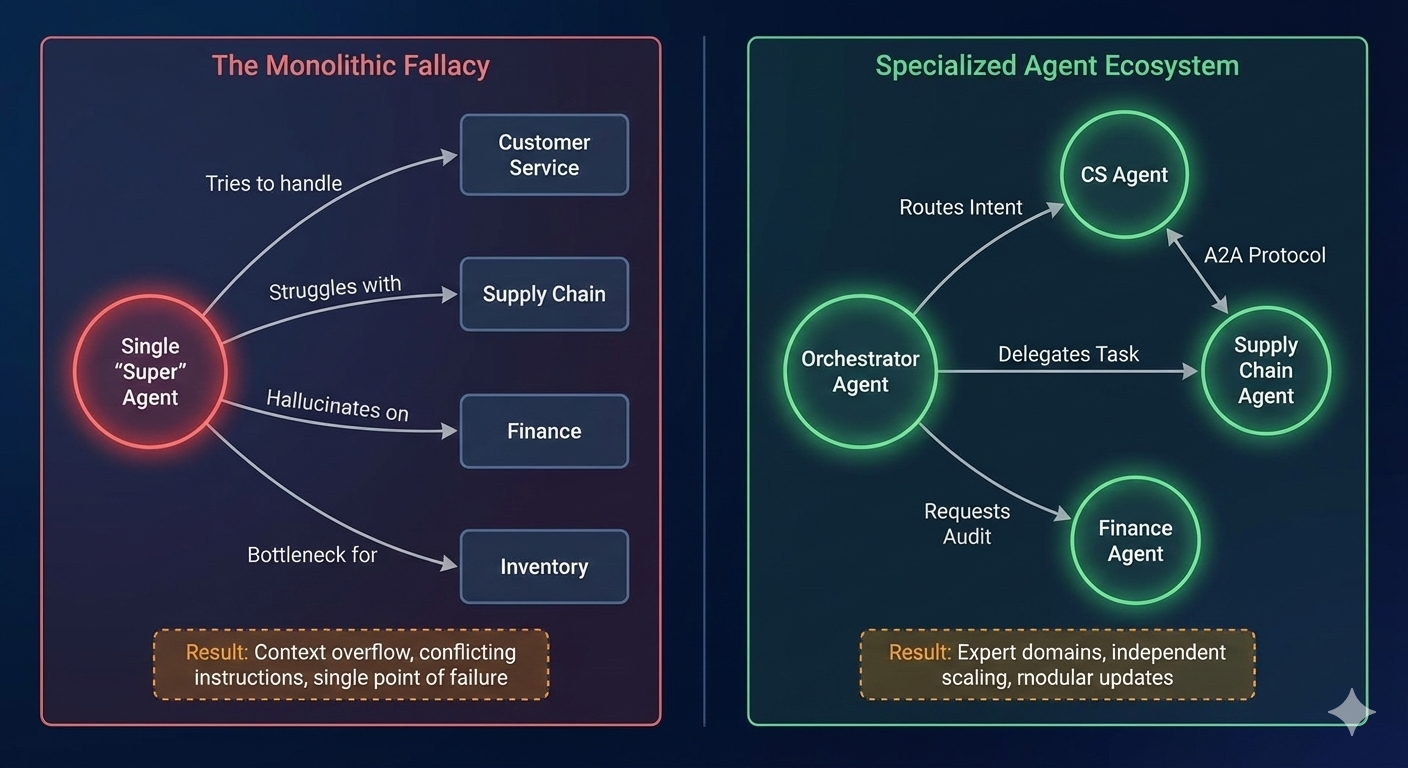
If you believe the vendor pitches, enterprise AI will soon be powered by a single, all-knowing agent platform from your favourite technology provider. Sales decks promise seamless integration, unlimited capabilities, and magical business transformation—just sign here and let their agents handle everything.
Reality check: This vision represents neither the future nor the optimal architecture for enterprise AI.
The future of enterprise AI will be powered by hundreds of specialised agents working together, not a single platform. Customer service requires different expertise than inventory management. Financial forecasting demands different frameworks than content generation. No single agent can handle this breadth while maintaining production-grade depth.
MACH as the Prerequisite: MACH architecture already established the composable infrastructure needed for flexibility. They've solved the hard problems of service discovery, API orchestration, distributed transactions, and failure handling that multi-agent systems also require. Enterprises with mature MACH implementations can plug in AI agents as specialised microservices rather than rearchitecting their entire technology stack.
organisations with composable MACH architectures are twice as likely to succeed with AI (77% vs 36% success rate).machalliance...
The numbers are sobering for those without this foundation. The primary culprit isn't the AI technology itself—it's the architectural impedance mismatch between monolithic systems and the composable, distributed nature of effective AI deployment.
Without open standards, the agent layer risks becoming the next lock-in layer. Once you've built hundreds of agents on a proprietary platform with months of interaction history, switching costs become prohibitive.
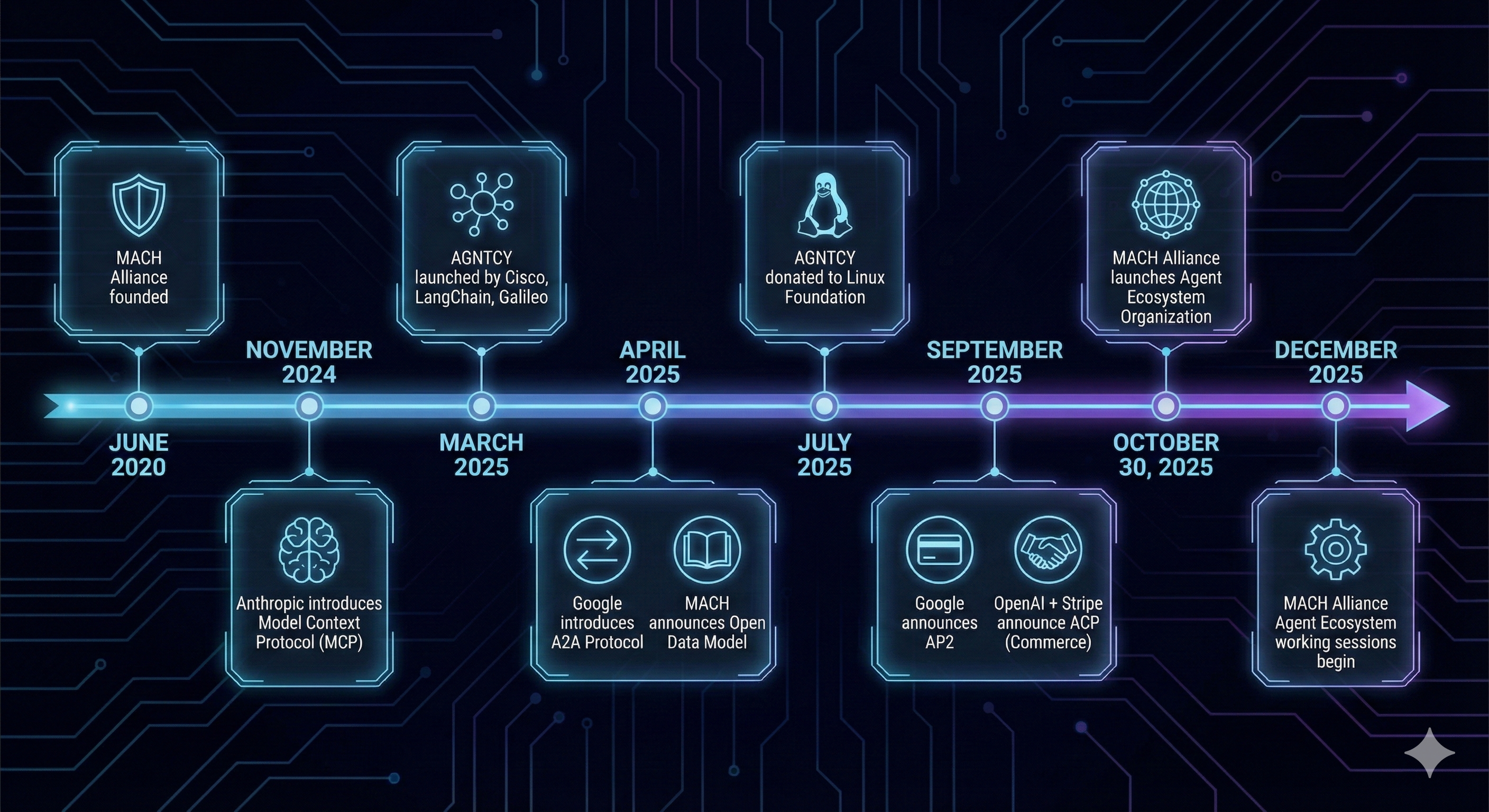
Three major initiatives—AGNTCY, open protocols (A2A, MCP, AP2), and the MACH Agent Ecosystem—are racing to define standards before proprietary walled gardens calcify.
The Three-Layer Agent Ecosystem Architecture
Here's the critical insight that most coverage misses: these initiatives aren't competing—they're building complementary layers of the same infrastructure stack.
If we take City Planning analogy: AGNTCY provides physical infrastructure (roads, electrical grid). Protocols are regulatory frameworks (traffic laws, building codes). MACH Agent Ecosystem is city planning that proves businesses can operate successfully using that infrastructure.
The emerging agent ecosystem follows a similar pattern:
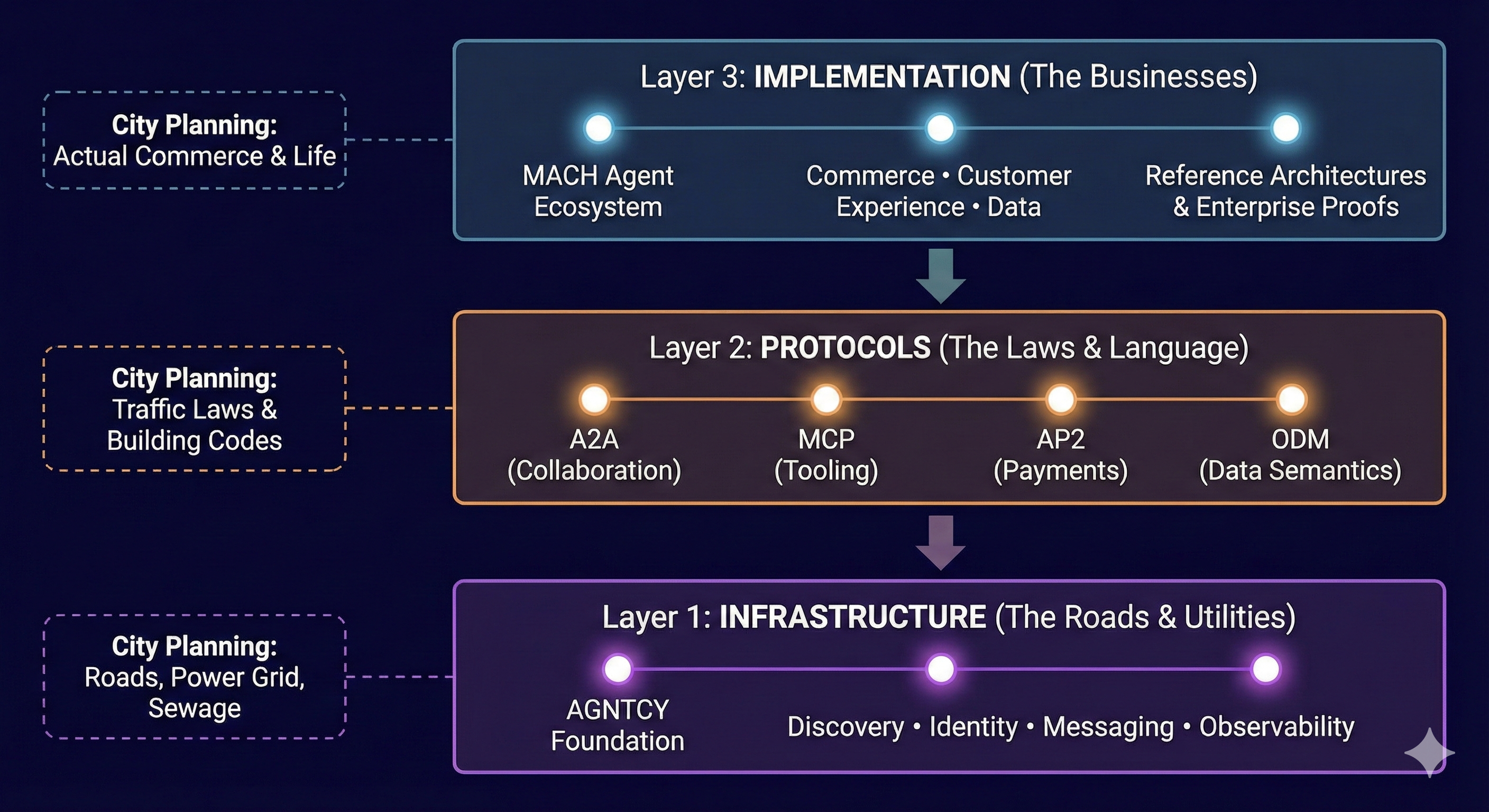
Layer 1: Infrastructure - AGNTCY
Founded by Cisco, LangChain, and Galileo, AGNCTY provides the open-source plumbing donated to the Linux Foundation: discovery, identity, messaging, observability.
Layer 2: Protocols - A2A, MCP, AP2, ODM
Protocols define the language for agent collaboration—how they communicate requests, negotiate capabilities, exchange data, and coordinate transactions. A2A for agent-to-agent collaboration, MCP for agent-to-tool connections, AP2 for payments, ODM for semantic interoperability.
Layer 3: Agent Ecosystem - MACH Alliance
Focuses on execution, co-creating reference architectures and enterprise proofs to ensure protocols work in production at scale with real workflows, real data, and real business requirements. Focused on commerce, customer experience, and customer data.
The strategic question isn't which initiative to pick, but how to leverage all three layers to build systems that avoid lock-in while maintaining the integration depth required for production operations.
AGNTCY – The Foundational Infrastructure
Mission: Building infrastructure for the "Internet of Agents"—agnostic to vendors, frameworks, and implementation choices.
Think of this as the TCP/IP and DNS layer for agents—the essential infrastructure that makes everything else possible. Without standardised discovery, agents can't find collaborators. Without verifiable identity, they can't trust each other. Without secure messaging, they can't exchange sensitive information. Without observability, debugging multi-agent workflows becomes impossible.
This is deliberately ambitious. The internet succeeded precisely because no single vendor controlled TCP/IP, DNS, or HTTP. Anyone could build compatible implementations. Innovation happened at the edges, not through centralised gatekeepers. AGNTCY aims to replicate this model for agent collaboration.
Governance Model: The donation to the Linux Foundation signals serious intent. The Technical Steering Committee includes representatives from Cisco, Dell, Red Hat, Oracle, and Google Cloud—companies with long-term infrastructure commitments and track records of contributing to open standards.linuxfoundation...
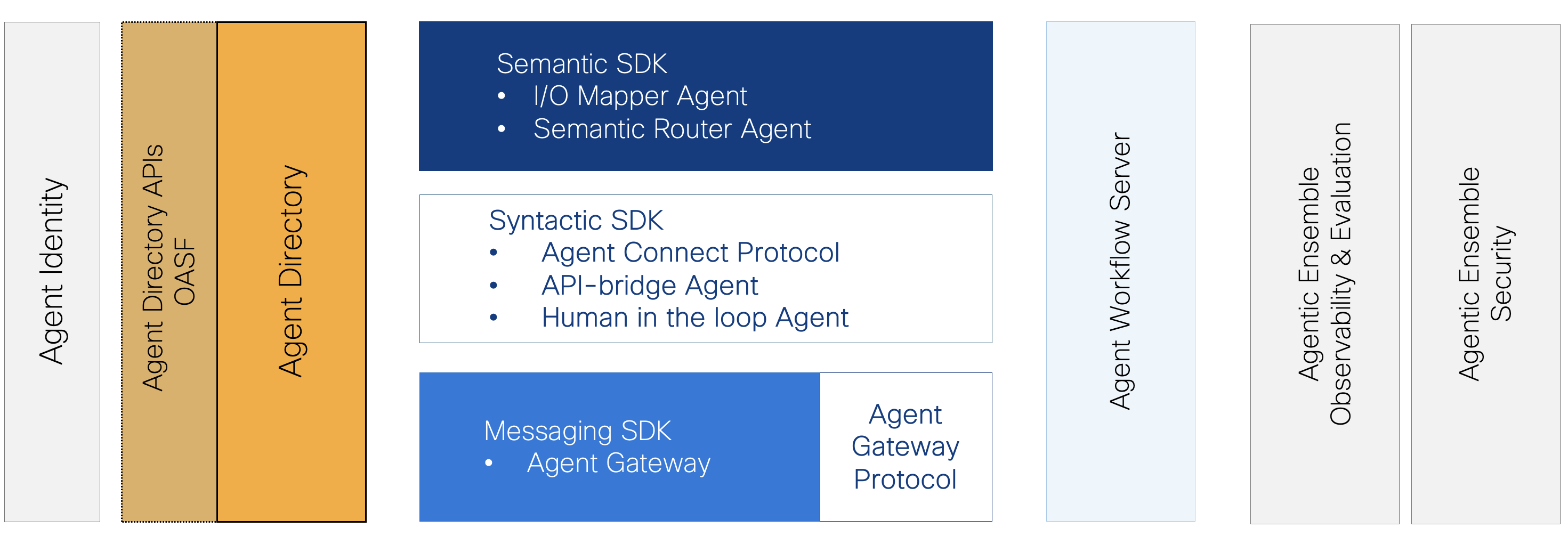
AGNTCY organises the multi-agent lifecycle around four phases, each with supporting infrastructure components:
DISCOVER: Find and Evaluate Agents
Components: Agent Directory, Open Agent Schema Framework (OASF)agntcy-oasf
The Agent Directory acts as the DNS for agents—a distributed registry where any organisation can publish and discover agents. OASF provides standardised metadata (built on OCI standards and Protocol Buffers) describing what agents can do, their inputs/outputs, and operational characteristics. Your customer service agent can dynamically discover inventory agents from different vendors without hard-coded integrations.
COMPOSE: Connect Agents into Workflows
Components: Agent Connect Protocol (ACP), Protocol Bridgesacp-spec
ACP standardises how agents communicate across different frameworks—handling authentication, context sharing, state management, and error handling. Protocol bridges enable LangGraph, CrewAI, and AutoGen agents to collaborate without rewriting existing systems. This is where A2A and MCP protocols integrate with AGNTCY's infrastructure.mcp-vs-acp
DEPLOY: Run Multi-Agent Systems at Scale
Components: SLIM Messaging, Identity Servicesslim-core
SLIM (Secure Low-latency Interactive Messaging) provides the transport layer with microsecond-level latencies (Rust data plane), quantum-safe cryptography, and multi-modal support. Identity Services offer cryptographically verifiable credentials using decentralised identity and Sigstore signing—moving security from implicit trust to explicit verification, critical for Know-Your-Agent (KYA) frameworks.
EVALUATE: Monitor and Improve Performance
Components: Observability Framework, Telemetry Servicesobserve-eval
Built on OpenTelemetry, provides distributed tracing specifically designed for multi-agent workflows. When five agents from three vendors collaborate and something fails, you need to see exactly where, which agent made which decisions, and what data was available at each step. Enables measuring outcomes, resolving bottlenecks, and fine-tuning agent collaboration based on real-world performance.
Production Status: SDKs in Python, JavaScript and Golang are available today. Reference implementation (CoffeeAgntcy) demonstrates all components working together in a fictitious coffee company multi-agent system.docs.agntcy.org
Protocols: The Language for Collaboration
For architects designing agent systems, understanding what each protocol actually does—and when to use it—is critical. Let's break down the technical characteristics:
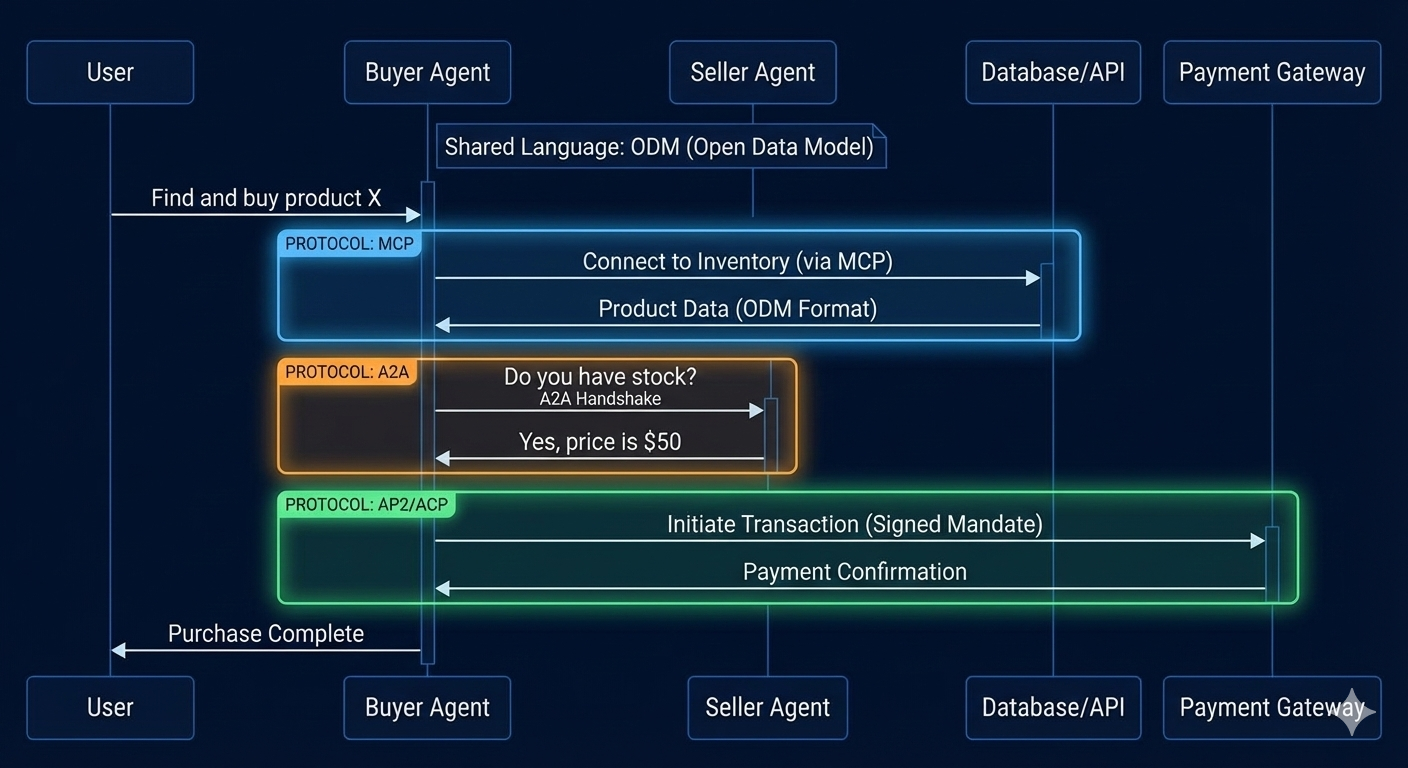
MCP (Model Context Protocol) - Anthropic
Purpose: Universal interface for agents to access tools and data sources
Transport: JSON-RPC 2.0 over stdio, streamable HTTP
Key Innovation: Separates "what a tool does" from "how it's implemented"
MCP solves a deceptively simple problem: every agent framework has its own way of integrating tools. LangChain uses one approach, LlamaIndex another, AutoGen yet another. MCP provides a standard interface so any tool can work with any agent framework.
Think of it as USB for agents—one connector that works everywhere. This abstraction layer is critical for composability. Without MCP: Every agent needs custom integration logic for every tool (N × M problem). With MCP: N agents use one protocol and M tools implement one interface.
Use it when: You're building agent-to-tool connections and want framework independence.
A2A (Agent-to-Agent Protocol) - Google → Linux Foundation
Purpose: Enable agents to discover and collaborate with each other
Transport: HTTPS, Streaming with Server-Sent Events (SSE), JSON-RPC
Key Innovation: "Agent Cards" for capability discovery
A2A focuses on the collaboration problem: How does your customer service agent find and work with a shipping agent it's never encountered before? Agent Cards provide standardised metadata describing capabilities, authentication requirements, and API contracts.
The protocol supports both request-response and streaming patterns, enabling everything from simple API calls to complex multi-turn conversations.
Use it when: Building multi-agent systems where agents need to dynamically discover and coordinate with each other.
ACP (Agent Connect Protocol) - AGNTCY → Linux Foundation
Purpose: Remote agent invocation with thread management
Transport: REST/OpenAPI
Key Innovation: First-class support for conversational threads and streaming
AGNTCY's ACP (not to be confused with the commerce protocol below—yes, the naming is confusing) provides a RESTful interface specifically designed for agent interactions. Unlike generic API calls, it understands the concept of conversational threads, partial responses, and human-in-the-loop approvals.
Available SDKs in Python and TypeScript make integration straightforward. The protocol is designed to work alongside A2A and MCP, not replace them.
Use it when: You need a simple, REST-based way to invoke remote agents with conversation management.
ACP (Agentic Commerce Protocol) - OpenAI + Stripe
Purpose: Secure commerce transactions between agents and merchants
Transport: HTTPS with webhook callbacks
Key Innovation: SharedPaymentToken for secure payment without exposing credentials
Yes, there are two protocols called "ACP"—welcome to the standards wars. This ACP handles the specific problem of commerce: how does an agent purchase something on your behalf without you giving it your credit card?
The protocol defines a complete commerce flow:
- Agent discovers merchant capabilities
- Cart creation with real-time pricing
- Secure payment token exchange (the SharedPaymentToken abstraction)
- Order processing with confirmation
- Post-checkout notifications and tracking
Use it when: Building agents that need to conduct commerce transactions securely.
AP2 (Agent Payments Protocol) - Google
Purpose: Payment authorisation specifically for agent transactions
Transport: Extension of A2A and MCP
Key Innovation: Cryptographic mandates for secure payment flows with 60+ financial partners
AP2 focuses specifically on the payment authorisation problem, working alongside the commerce protocols above. It provides secure payment flows with major payment networks—Mastercard, PayPal, Visa, and others.
The cryptographic mandate system ensures that agents can't make unauthorised payments even if compromised. This is critical for enterprise adoption.
Use it when: Implementing payment flows in agent systems with enterprise-grade security requirements.
ODM (Open Data Model) - MACH Alliance
Category: Data Standard (not a protocol)Purpose: Semantic interoperability - the "Rosetta Stone" for agent data
Key Innovation: Canonical reference models for common business entities
Covers: Customer, Order, Product, Payment, Inventory, Fulfilment, and dozens more
ODM solves the comprehension problem that protocols can't: two agents can exchange messages perfectly via A2A or MCP, but without shared data models, they can't understand each other. One agent uses customer_id, first_name; another uses cust_num, given_name. ODM provides the standard schemas that make communication meaningful, not just possible.
Use it when: Building multi-vendor agent systems where data understanding (not just data exchange) is critical—especially in commerce, customer data, and experience workflows.
Key Distinction: Protocols enable communication; ODM enables comprehension.
MACH Agent Ecosystem: Proving Production Viability
The MACH Alliance's Agent Ecosystem addresses a critical gap: the difference between standards that work in theory and standards that work in production.
The focus on co-creating reference architectures and enterprise proofs throughout 2026 targets this gap directly:
- Reference architectures demonstrate patterns that work
- Enterprise proofs validate performance at scale
- Operating patterns capture lessons learned from production deployments
Without this execution focus, agent standards risk becoming another pile of specifications that look great in whitepapers but fail in production due to edge cases, performance problems, or operational complexity that only surfaces at scale.
MACH Foundations: Composable Architecture as Prerequisite
Composable architecture provides the stability and flexibility required for agent integration. organisations with mature MACH implementations have already solved the hard problems of:
- Service discovery
- API orchestration
- Distributed transactions
- Failure handling
They can add agent capabilities incrementally using existing DevOps tooling, CI/CD pipelines, and governance frameworks rather than requiring agent-specific platforms.
Incremental Evolution: This foundation enables AI capabilities to be evolved incrementally without vendor lock-in. Rather than rearchitecting entire systems, you can add agent capabilities to existing APIs, expose new agent interfaces alongside traditional endpoints, and experiment with agent patterns without breaking existing workflows.
This approach treats agents as specialised microservices within the broader composable architecture rather than requiring separate "agent platforms" with their own operational patterns and governance frameworks.
Focus Areas
Early efforts concentrate on experience, customer data, and commerce infrastructure—strategic choices that maximise impact while providing clear success criteria.
- Customer Experience: Multi-agent workflows for customer service, personalisation, and engagement provide immediately visible business value. Customers notice better service. Revenue teams track improved conversion. Success is measurable, not speculative.
- Customer Data: Unified customer profiles aggregated from multiple sources demonstrate the power of semantic interoperability through ODM. When agents from different vendors can all understand and update a shared customer model, data quality and consistency improve dramatically.
- Commerce Infrastructure: Order management, inventory coordination, payment processing, and fulfilment workflows involve multiple systems that must coordinate reliably. Proving agent interoperability in commerce validates the approach for other high-stakes workflows.
These aren't random selections—they're high-value use cases where interoperability directly impacts business outcomes and where failure is obvious rather than subtle.
Who's Actually Involved
The participant list reveals serious enterprise commitment across multiple categories:
- Hyperscalers: AWS, Google Cloud (notably absent: Microsoft Azure, though they may join later)
- Systems Integrators: Accenture Song, Deloitte Digital, Publicis Sapient, Valtech, WPP—the firms actually implementing enterprise AI at scale
- Commerce Platforms: commercetools, Stripe, Commerce Layer, Kibo—companies with real transaction volumes and enterprise customers
- Data & personalisation: Bloomreach, Amplitude, Coveo, Dynamic Yield—bringing the customer data layer
- Integration Specialists: Workato, Zapier, Pipe17, Patchworks—solving the "last mile" connection problem
This isn't a vendor marketing coalition. These are the companies/enterprises that actually depend on for revenue-generating systems. When they commit to interoperability standards, it means something.
Governance and Security: The KYA Imperative
Autonomous Agent systems introduce fundamentally new security challenges that traditional approaches don't address. Understanding and mitigating these risks is essential for production deployments.
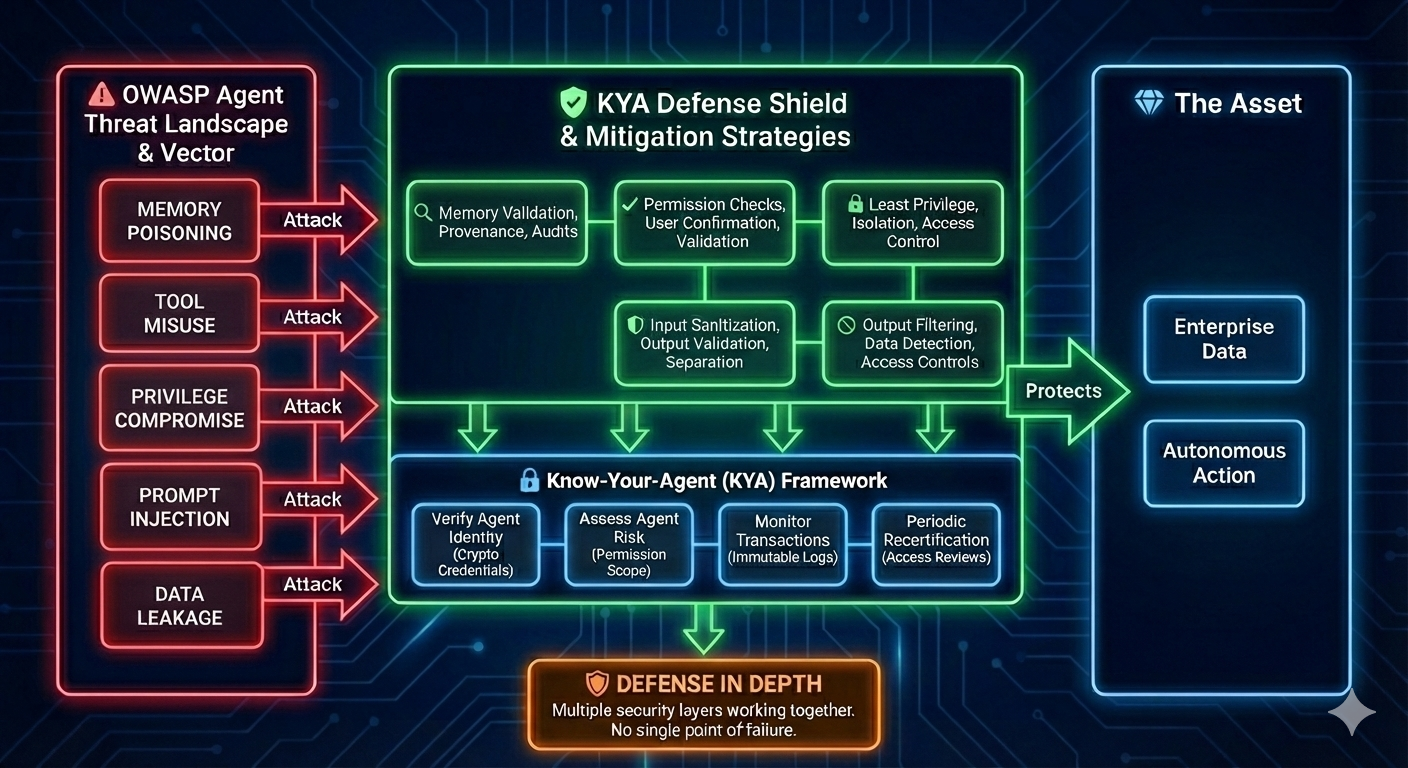
The New Threat Surface: Persistent State and Unpredictable Execution
Autonomous agents introduce new risks due to persistent state and unpredictable execution patterns. Unlike traditional software with deterministic behaviour and stateless processing, agents maintain context across interactions, make autonomous decisions, and exhibit emergent behaviours that are difficult to predict or audit.
Traditional security—perimeter defence, access control, static analysis—proves insufficient because the threat vectors are qualitatively different:
- Memory Poisoning: Agents rely on accumulated knowledge and conversation history to inform decisions. Corrupting this long-term memory can influence future behaviour in subtle, hard-to-detect ways. An attacker who poisons an agent's memory with false information about approved vendors or pricing policies can manipulate business decisions long after the initial compromise.
- Tool Misuse: Agents invoke tools and APIs on behalf of users. Without strict validation, malicious prompts can manipulate agents into invoking tools in unintended ways—extracting sensitive data, modifying configurations, or initiating unauthorised transactions.
- Privilege Compromise: Agents often receive elevated privileges to accomplish tasks on behalf of users. Attackers who compromise agent credentials or execution contexts can escalate privileges far beyond the original user's authorisation.
These aren't theoretical vulnerabilities—they're documented threats in the OWASP Top 10 for LLM Applications and Agents. Production deployments must address them explicitly rather than assuming traditional security suffices.
The KYA Imperative
Security requires moving from Know-Your-Customer (KYC) to Know-Your-Agent (KYA), demanding systems that verify and audit the identity and authorisation of agents themselves.
- Verify Agent Identity: Use cryptographic credentials to confirm that an agent is who it claims to be, issued by a trusted authority, and hasn't been tampered with since issuance.
- Assess Agent Risk: Evaluate the scope of an agent's permissions, the sensitivity of data it can access, and the potential impact of compromise. Not all agents require the same level of scrutiny.
- Monitor Agent Transactions: Track all actions agents take, maintain immutable audit logs, and alert on anomalous patterns that might indicate compromise or misuse.
- Periodic Recertification: Regularly reassess whether agents still require their current privilege levels, similar to how access reviews ensure humans don't accumulate unnecessary permissions over time.
KYA isn't just good security practice—it's essential for regulatory compliance in finance, healthcare, and other regulated industries where accountability for automated decisions has legal implications.
Critical Risks: The OWASP Agent Threat Landscape
Technical leaders must mitigate specific threats documented in the OWASP Agents AI Threats framework:
| Threat | Impact | Mitigation |
|---|---|---|
| Memory Poisoning | Corrupting long-term memory influences future decisions | Memory validation, provenance tracking, periodic audits |
| Tool Misuse | Manipulating agents into unintended tool invocations | Permission checks before every tool call, explicit user confirmation |
| Privilege Compromise | Escalating agent access beyond authorised scope | Principle of least privilege, execution isolation |
| Prompt Injection | Crafting inputs that override intended behaviour | Input sanitisation, output validation, instruction separation |
| Data Leakage | Exposing sensitive information through responses | Output filtering, sensitive data detection, access controls. |
Strategic Decision Framework for Technical Leaders
Moving from understanding to action requires a framework for making architectural decisions about agent systems.
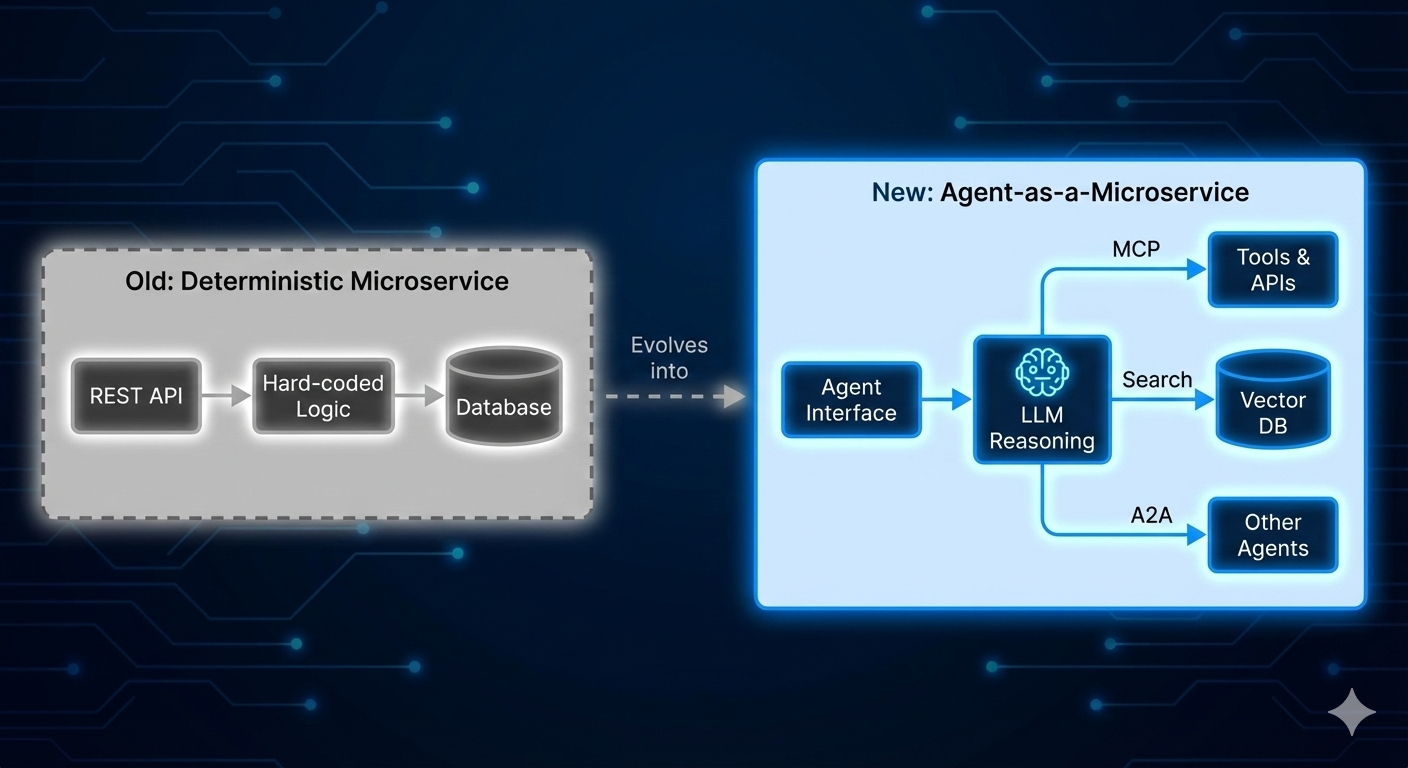
Adopt Agent-as-a-Microservice (AaaM)
Design multi-agent systems using the Agent-as-a-Microservice blueprint. This architectural pattern treats agents as specialised microservices within your existing infrastructure rather than requiring separate "agent platforms."
The AaaM Advantage:
- Leverage existing DevOps tooling for deployment and monitoring
- Apply established governance structures already developed for MACH systems
- Use familiar patterns for service discovery, API design, and failure handling
- Integrate agents incrementally without rearchitecting entire systems
Build vs. Participate
AGNTCY: Open source, production-ready SDKs available today
Agent Ecosystem: Formation phase—strategic window to influence outcomes
Avoid Proprietary Lock-In
Decouple architectural components to maintain strategic optionality:
- Decouple Agent Memory from Goals
- Separate UI Interfaces from Logic Layers
- Use Open Protocols for Communication
- Maintain Abstract Service Boundaries
- Document Explicitly, Integrate Loosely
These engineering patterns preserve optionality as the agent ecosystem evolves.
Risks, Uncertainties, and Watch Items
Let's be honest about maturity and risks. This is cutting-edge technology, and not everything is production-ready.
Maturity Reality Check
AGNTCY: Active development with SDKs available, but no published production metrics or case studies from major enterprises. The "reference implementations" like CoffeeAgntcy are educational examples, not battle-tested production systems.
Agent Ecosystem: Less than 2 months old. Currently in coalition-building phase, not production deployment phase. The "45+ technology providers" are expressing interest, not committing engineering resources yet.
AP2: Google's own language admits that consumer implementations "have yet to launch." B2B implementations are further along but still early.
Open Data Model: In development for 3+ years before initial release, suggesting this is harder than it looks. Current coverage of business entities is limited.
Open Questions That Matter
Will A2A and AGNTCY's ACP converge?
IBM's technical analysis suggests possible convergence, as both solve similar problems (agent invocation and coordination) with different approaches. The Linux Foundation governance model could facilitate this, but organisational dynamics often prevent technical consolidation even when it makes sense.
How will proprietary platforms integrate?
Salesforce Agentforce, Microsoft Copilot, and other proprietary agent platforms have announced support for "open standards," but details are vague. Will they implement full protocol compatibility, or just minimal API bridges that maintain their walled gardens?
What enforcement mechanisms ensure true interoperability?
Standards are great, but vendor implementations often diverge over time. Who validates compliance? What happens when Vendor A's A2A implementation doesn't actually interoperate with Vendor B's?
What about data privacy and consent?
Agents collaborating across organisational boundaries need to respect data privacy regulations (GDPR, CCPA, etc.) and user consent. The protocols define technical mechanisms, but governance frameworks for multi-organisation agent collaboration are still immature.
Items to Watch in 2025-2026
Linux Foundation governance decisions
Watch for announcements about coordination between A2A and AGNTCY projects. Consolidation would strengthen both; continued fragmentation would weaken adoption.
First enterprise-scale proofs from Agent Ecosystem
The MACH Alliance has promised reference implementations and production proofs throughout 2026. These will reveal whether the architecture works at scale or if there are hidden integration challenges.
Payment network adoption of AP2
Mastercard and PayPal are partners, but have they actually implemented AP2 support in production systems? Track announcements about real transaction volume flowing through AP2.
Microsoft's agent strategy
Microsoft is conspicuously absent from these initiatives. Given their market position (Azure, Copilot, GitHub), their strategy will significantly impact adoption. Watch for announcements about whether they embrace open standards or build proprietary alternatives.
Vendor consolidation
75+ companies in AGNTCY sounds impressive, but how many will still be active contributors in 12 months? Open source governance often starts with big coalitions that shrink to a core group of committed contributors.
Conclusion: The Strategic Window Is Now
Three critical takeaways for technical leaders navigating the agent ecosystem landscape:
1. The Infrastructure Layer Is Solidifying
AGNTCY under Linux Foundation governance provides credible, neutral foundation with production-ready SDKs. The fundamental problems of discovery, identity, messaging, and observability must be solved by any serious multi-agent architecture.
2. Enterprise Implementation Proves Theory
MACH Agent Ecosystem focuses on proving standards work at scale. Reference architectures and enterprise proofs in high-value domains (commerce, CX) will determine whether these standards deliver or remain academic.
3. Technical Leaders Must Act
Standards are set by those who show up. The next 12-18 months will define patterns for the next decade.
Immediate Actions:
- Experiment with AGNTCY SDKs now
- Design systems with open protocol support
- Adopt Agent-as-a-Microservice patterns
- Participate in working groups
- Avoid platforms without interoperability guarantees
Historical Parallel: In the 1990s, enterprises that bet on proprietary networks (AOL, CompuServe) had to rebuild. Those who bet on TCP/IP and HTTP built lasting value. Open standards win in the long run when backed by credible governance and strong coalitions.
"Just like when the cloud and the internet came about and accelerated applications and social interactions at a global scale, we want to build the Internet of Agents that accelerates all of human work at a global scale." — Vijoy Pandey, VP of Engineering at Cisco's Outshift
That future is being built today by organisations willing to collaborate on open standards rather than compete on proprietary implementations.
The strategic window for shaping that future is now.
Timeline of Major Events
Further Reading and Resources
Primary Sources
- AGNTCY: agntcy.org | docs.agntcy.org | github.com/agntcy
- Agent Ecosystem: agentecosystem.org
- MACH Alliance: machalliance.org
- A2A Protocol: a2aprotocol.ai
- Open Data Model: github.com/machalliance/standards
Key Protocol Documentation
- MCP (Anthropic): modelcontextprotocol.io
- Agentic Commerce Protocol: agentic-commerce-protocol.com
- Agent Payments Protocol: Google Cloud Blog announcements
Technical Implementation Guides
- CoffeeAgntcy Reference Implementation: github.com/agntcy/coffeeAgntcy
- AGNTCY Component Quickstarts: SLIM, Identity, Agent Directory guides at docs.agntcy.org
Follow me on LinkedIn for more insights on AI architecture, cloud engineering, and emerging technology standards.
Last updated: December 2025
Also published on Medium - Join the discussion in the comments!
